Cookie stuffing directly impacts the bottom line of a publisher. Learn everything about cookie stuffing here:
Ad fraud remains a concern for adtech publishers and advertisers. The Cooking stuffing practice is one such popular practice that came into the picture in 2008 when eBay went after Shawn Hogan in a multi-million dollar lawsuit that ended with him in jail.
Before we explain what is cookie stuffing is, let’s first take a look at terms like affiliate marketing (we will be using them a lot) and cookies.
What is Affiliate Marketing?
Affiliate marketing is a method for publishers to make money with decent traffic on their websites. Just like adtech, the affiliate market deals fraud. And things have been tough for publishers due to the increase in ad fraud.
For affiliate marketing publishers, cookie stuffing is the biggest threat to their earnings. This practice takes away the credit publishers deserve from their website traffic and users.
To understand cookie stuffing let’s start by knowing cookies and affiliate marketing. Cookies are a piece of code that store (remember) information on the web. For example, a cookie remembers the last time you visited a website and item you placed on your cart to purchase on eCommerce site.
Basically, cookies help sites create a user mapping and remember their actions on a specific site.
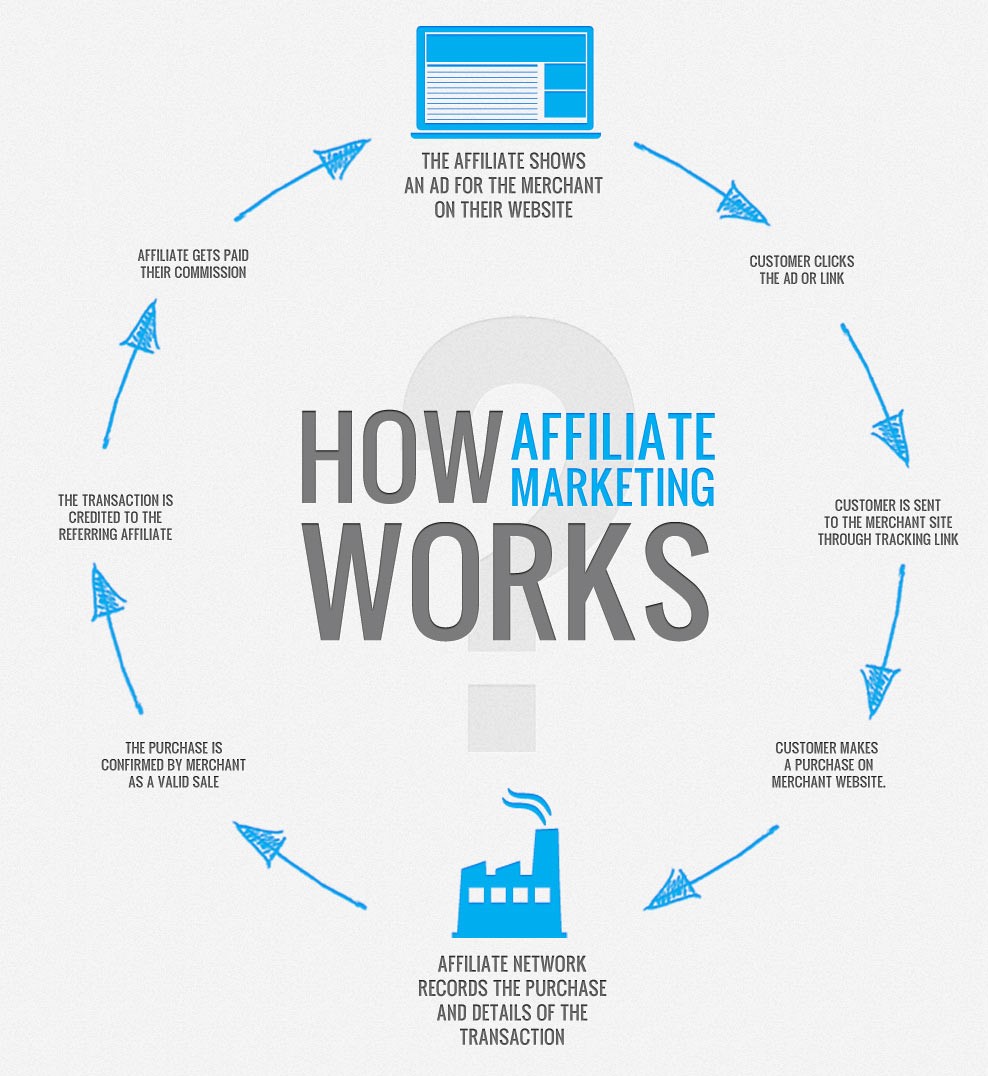
Next, affiliate marketing. Some websites (especially eCommerce) share a part of their earnings with publishers who agree to divert a few visitors to their sites. This is done by adding a link to the publisher site that takes the user to eCommerce site.
If a user makes a purchase using this link then the publisher gets a percentage of the sale. Here, the identity of the users and their internet activity are stored using cookies.
Unfortunately, cookies and affiliate marketing are often used together in case of a fraud—cookie stuffing.
What is Cookie Stuffing?
When a user clicks on an affiliate link on a publisher’s site, the credit (money) for that click goes to a fraudster rather than the publisher. This fraud is carried out by stuffing or dropping cookies.
Cookie stuffing got industry-wide attention when Shawn Hogan scammed eBay a sum of $28 million in 2008. Shawn was a marketer, who dropped several malicious cookies to the user’s browser.
After which, every time these users clicked on the affiliate eBay links, Shawn made money (sales were attributed to him).
Cookie stuffing is a common sharp practice on online coupon sites. Here fraudsters place a handful of cookies to the user browsers to claim credit for online purchases made by users.
How Are Cookies Dropped
Here are the methods used by fraudsters to drop cookies on the user’s browser:
- Pop-ups:
A pop-up on its own is a harmless dialog box used to notify users about offers. However, malicious pop-ups are capable of sending malware to browsers as soon as the user interacts with it. For that, users need to be careful with the use of third-party popup apps or extensions on web browsers.
- JavaScript:
JavaScript is used to make webpages more attractive and interactive. It is also used to redirect users to a different webpage. For fraudsters, it gets easy to push a malicious code between the redirects. If you, as a publisher, have noticed any such link on your site then remove and report it.
- iFrame:
It is used to add HTML code inside another HTML code. Generally, this technology is used to place ads on websites. Where advertisers are given a section on the website to place their creative codes. Adding a third-party code to site can be risky at times. Hence, publishers are recommended to use Safe Frames on the website, which disallow malicious code and manipulation of content.
How does this Affect Publishers?
The publisher who takes the help of affiliate marketing experiences the most loss. Due to cookie stuffing, they don’t get to bag the credit they have for certain clicks and conversions on eCommerce site, while fraudster steals money from them.
What about the non-affiliate publishers?
Non-affiliate publishers have a list of ad frauds to deal with. Most publishers go for both ads and affiliate links to better monetize everything. However, if we specifically talk about only display ads, ad revenue is also harmed by dropping cookies to the user’s site. Just like affiliate links, cookie dropping snatches the credit from clicks/impressions on ad.
However, due to the complex supply chain involved to sell an impression, cookie stuffing hasn’t affected this area as much as the affiliate market.
How to Eliminate This Problem?
Be it fake publishers dropping malicious scripts or users installing fraudulent extensions, cookie stuffing is bad for business. And eliminating it entirely is easier said than done.
Large-scale cookie stuffing fraud like the one pulled off by Shawn Hogan is easily identifiable now. Because eCommerce businesses are now tracking unusual affiliate activities by tracking conversion rates and site redirects.
But this technique requires constant tracking and data. Meaning, unless the scam is of Amazon or eBay level, it will not be identified as easily.
The malicious cookies are dropped on the user’s browser. Meaning, publishers can do the least from their sides to make this right. Since the malware that steals the affiliate from publishers is also capable of stealing user’s data and even passwords. Publishers can work on alerting users about the scam. While users need to be careful with the clicks they are making.
Key Takeaways:
- Cookies are small files which carry data specific to a particular website or user. This data can be accessed either by the web server or the user’s computer.
- Affiliate marketing is a method for publishers to make money with decent traffic on their websites. Just like adtech, the affiliate market deals with fraud. And things have been tough for publishers due to the increase in ad fraud.
- Cookie stuffing is a common sharp practice on online coupon sites. Here fraudsters place a handful of cookies to the user browsers to claim credit for online purchases made by users.
- Publishers and users are duped to install malicious extensions and integrate questionable scripts through pop-ups or java script.
- Cookie stuffing directly impacts the publisher’s revenue. Whether it is a publisher running a cookie dropping script unintentionally or a user installing a corrupt extension, it ends up affecting the publisher’s affiliate revenue.
FAQs
Referring a product or service through a blog, social media platform, podcast, or website is affiliate marketing. Each time someone purchases through the affiliate link associated with their recommendation, the affiliate earns a commission.
Visit a suspect site, clear the cookies off your browser, and then see what cookies were dropped on you. Since you haven’t clicked on anything, any click cookies have been stuffed.
The practice of cookie stuffing (also known as cookie dropping) involves a third-party dropping multiple affiliate cookies on a user’s browser in order to claim commissions on sales. “Cookie stuffing leads to wrongful attribution”

Shubham is a digital marketer with rich experience working in the advertisement technology industry. He has vast experience in the programmatic industry, driving business strategy and scaling functions including but not limited to growth and marketing, Operations, process optimization, and Sales.